It has been discovered that malware was embedded in the long-established virtual drive software 'DAEMON Tools,' and that it was officially distributed for nearly a month without being noticed.
It has been revealed that malware was embedded in the official installer of the long-established disk image mounting software ' DAEMON Tools Lite '. According to security company Kaspersky, the tampering began on April 8, 2026, and the developer, Disc Soft Limited, has acknowledged the problem and released version 12.6.0.2445, which does not contain the malware.
Popular DAEMON Tools software compromised | Securelist
Security Incident Affecting DAEMON Tools Lite: What We Know So Far
https://blog.daemon-tools.cc/jpn/post/security-incident
Widely used Daemon Tools disk app backdoored in monthlong supply-chain attack - Ars Technica
https://arstechnica.com/security/2026/05/widely-used-daemon-tools-disk-app-backdoored-in-monthlong-supply-chain-attack/
DAEMON Tools devs confirm breach, release malware-free version
https://www.bleepingcomputer.com/news/security/daemon-tools-devs-confirm-breach-release-malware-free-version/
In May 2026, Kaspersky confirmed that installers distributed from the official DAEMON Tools website and signed with the developer's digital certificate contained a malicious payload. The affected versions of DAEMON Tools Lite were 12.5.0.2421 through 12.5.0.2434, and it is believed to have been a supply chain attack in which software obtained through normal official distribution channels became the source of infection.
Together with @bzvr_ , @2igosha and Anton Kargin, we identified that the DAEMON Tools software has been compromised in a complex supply chain attack since April 8. We see thousands of infections across 100+ countries. If you use DAEMON Tools, run a malware scan immediately! [1/7] pic.twitter.com/Gh3vEPDkgZ
— Georgy Kucherin (@kucher1n) May 5, 2026
The attackers tampered with binaries such as 'DTHelper.exe,' 'DiscSoftBusServiceLite.exe,' and 'DTShellHlp.exe' within the installed DAEMON Tools Lite. These files were placed in the DAEMON Tools Lite installation directory and bore the signature of the developer, 'AVB Disc Soft,' making them appear to users as legitimate software.
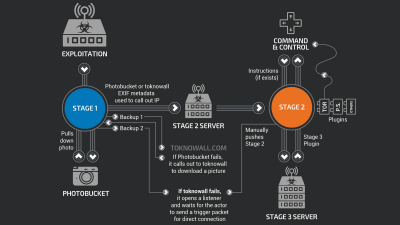
When the tampered binary is executed, such as during PC startup, a hidden backdoor is activated, and communication is sent to a server controlled by the attacker. The destination domain is a typosquatting domain that resembles the legitimate 'daemon-tools.cc,' and it is believed to have been registered on March 27, about a week before the supply chain attack began.
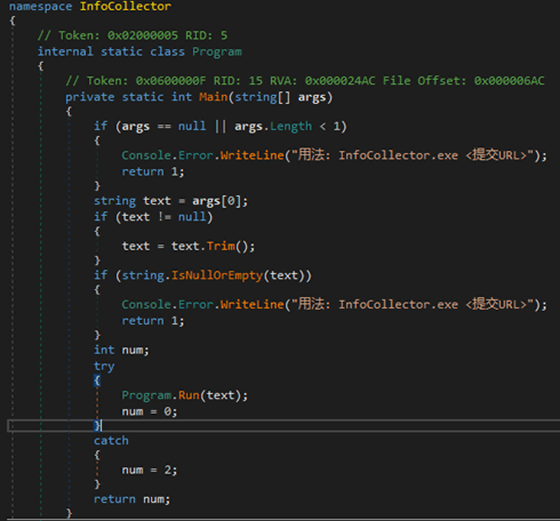
The initial payload deployed was malware designed for information gathering, collecting MAC addresses, hostnames, DNS domain names, running processes, installed software, and system locale. Kaspersky believes this information was used to screen infected devices, and based on those results, additional payloads were sent to some devices.
The following is a screenshot of the information gathering code containing Chinese characters.
Kaspersky telemetry detected thousands of attempts to deploy payloads via DAEMON Tools, affecting individuals and organizations in over 100 countries and regions, including Russia, Brazil, Turkey, Spain, France, Italy, and China. However, only about a dozen devices received additional payloads, and the targets were government organizations, research institutions, and manufacturing and retail companies in Russia, Belarus, and Thailand, suggesting the attacks were targeted.
One of the additional payloads identified was a lightweight backdoor capable of downloading files, executing shell commands, and running shellcode in memory. Furthermore, a terminal belonging to a Russian educational institution also contained a 'QUIC RAT' that supported multiple communication methods including HTTP, UDP, TCP, WSS, QUIC, DNS, and HTTP/3, and could inject payloads into notepad.exe and conhost.exe.
Kaspersky points out that the DAEMON Tools breach was highly organized and took about a month to detect, comparable to past large-scale supply chain attacks. They also noted that the attack was difficult for ordinary users to detect in advance, as infection could occur simply by installing software distributed from the official website and bearing a legitimate digital signature.
Disc Soft Limited explained that an internal investigation revealed unauthorized interference with its infrastructure, affecting some installation packages within its build environment. The company reported that within 12 hours of receiving notification around 7:00 AM on May 5th, it isolated the affected systems, deleted distribution files, audited the build and release process, rebuilt and verified the installer, and strengthened monitoring.
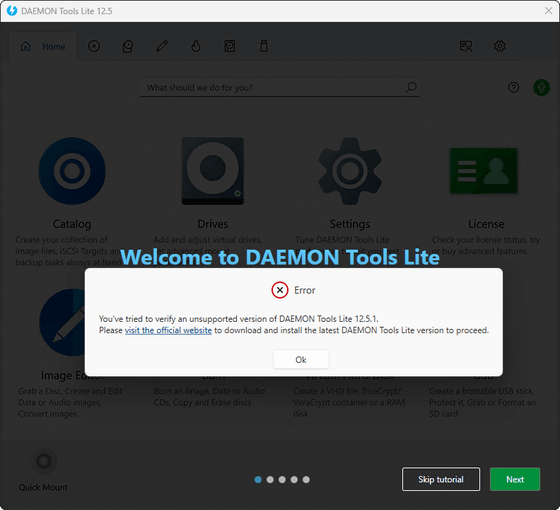
According to Disc Soft Limited, the problematic version 12.5.1 has been removed and is no longer supported. The company states that the problematic behavior has not been observed in DAEMON Tools Lite 12.6, released on May 5th, or in the latest version 12.6.0.2445, and that there is no continuing risk as long as the latest version is obtained from official sources.
Disc Soft Limited states that the impact is limited to the free version of DAEMON Tools Lite and does not affect DAEMON Tools Ultra, DAEMON Tools Pro, or other products. Users who downloaded or installed the free version of DAEMON Tools Lite 12.5.1 during the affected period are advised to uninstall the app, perform a full scan with reliable security software, and then obtain the latest version of DAEMON Tools Lite 12.6 from the official website.
Related Posts: