AirSnitch, a Wi-Fi attack technique that bypasses client isolation, exposes Wi-Fi networks to man-in-the-middle attacks

A group of researchers from the University of California, Riverside, and the Catholic University of Leuven in the United States has reported an attack method called ' AirSnitch ' that bypasses 'client isolation,' which blocks direct communication between clients on Wi-Fi networks. The research team investigated 11 major types of routers and networks, and found that at least one attack method was effective on all test targets.
AirSnitch: Demystifying and Breaking Client Isolation in Wi-Fi Networks - NDSS Symposium
GitHub - vanhoefm/airsnitch
https://github.com/vanhoefm/airsnitch
New AirSnitch attack bypasses Wi-Fi encryption in homes, offices, and enterprises - Ars Technica
https://arstechnica.com/security/2026/02/new-airsnitch-attack-breaks-wi-fi-encryption-in-homes-offices-and-enterprises/
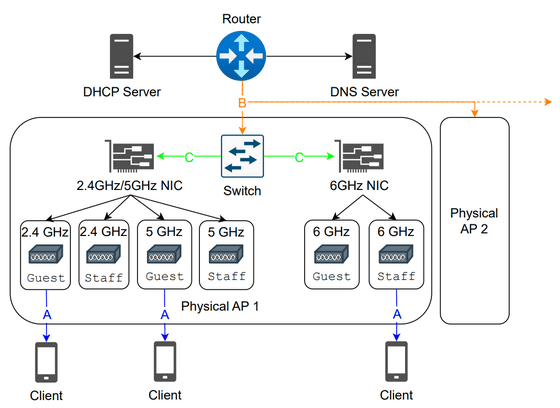
A modern Wi-Fi network architecture is shown below: A router connects a physical access point (AP) to the internet, DNS, and DHCP, allowing a single device to provide multiple virtual SSIDs via the AP's internal wireless NIC and switch.
The researchers say AirSnitch offers a practical and versatile alternative to enabling man-in-the-middle (MitM) attacks on modern Wi-Fi networks, and that it 'fundamentally undermines the security of client isolation, which has traditionally been considered an effective countermeasure against
The first is the abuse of the GTK (Group Temporal Key). Wi-Fi networks use a GTK shared by all clients in the network to encrypt broadcast and multicast traffic. The attacker has access to this shared key because they are also connected to the network as a legitimate user.
By exploiting this mechanism, an attacker can inject packets with the Wi-Fi layer destination set to a broadcast address (ff:ff:ff:ff:ff:ff) and the IP layer destination set to a specific victim. All tested operating systems have specifications that process unicast IP packets contained within broadcast packets, which allows them to bypass client isolation and send packets directly to the victim.
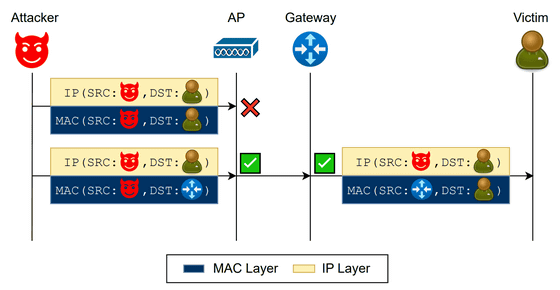
The second technique is called 'gateway bouncing,' which exploits the flaw that many Wi-Fi devices enforce client isolation only at the MAC (data link) layer, and not all the way up to the IP (network) layer.
The attacker sends packets with the destination MAC address set to that of the router (default gateway) and the destination IP address set to that of the victim. The access point's MAC layer separation function determines that the packets are destined for the gateway and allows communication, but the gateway then routes the packets at the IP layer, ultimately forwarding them to the victim's client. This allows packets to be exchanged between clients that should otherwise be blocked from direct communication.
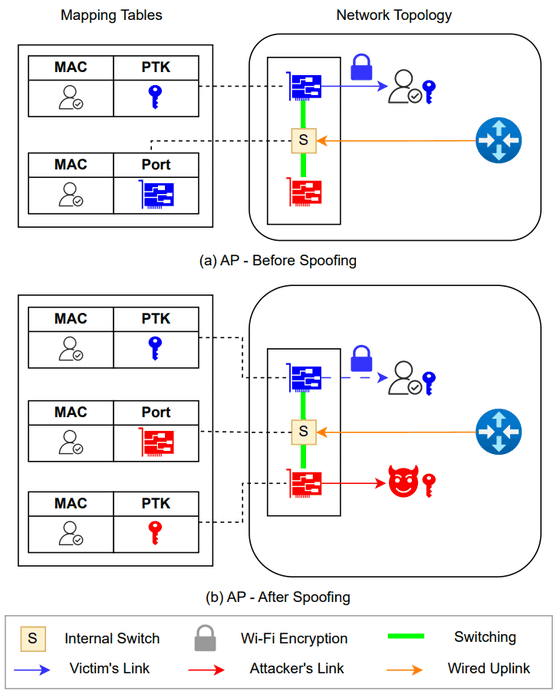
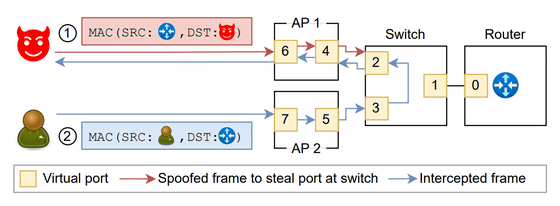
The third is 'traffic hijacking through port theft,' an attack method that manipulates the MAC address tables of switches and bridges within the network to divert communications intended for the victim to the attacker.
In this attack, the attacker spoofs the victim's MAC address and connects to a different access point or BSSID, rewriting the mapping on the switch so that data intended for the victim is received by the attacker's own device. Meanwhile, on the uplink, the attacker spoofs the MAC address of the network gateway, so that data the victim attempts to send to the Internet is sent to the attacker, who is the fake gateway.
The researchers report that by building on these techniques and combining them with additional techniques, they can bypass the blocking of communication from the guest network to the main network, enabling a complete two-way man-in-the-middle attack on home routers and corporate networks.
It also allows for the theft of authentication cookies, passwords, and payment information over unencrypted HTTP communications, and even when HTTPS is deployed, it can launch attacks such as DNS cache poisoning. Furthermore, it has been pointed out that there is a risk that attacks could intercept
The research team suggests countermeasures such as randomizing group keys, blocking unicast IP packets within broadcast Wi-Fi frames, using different GTKs or IGTKs for each VLAN and configuring appropriate firewall rules, preventing MAC and IP address spoofing, and centralizing Wi-Fi decryption and routing as needed. However, some vulnerabilities are related to the underlying hardware or implementation, and fixes may require design changes or standardization.
Related Posts:
in Security, Posted by log1i_yk